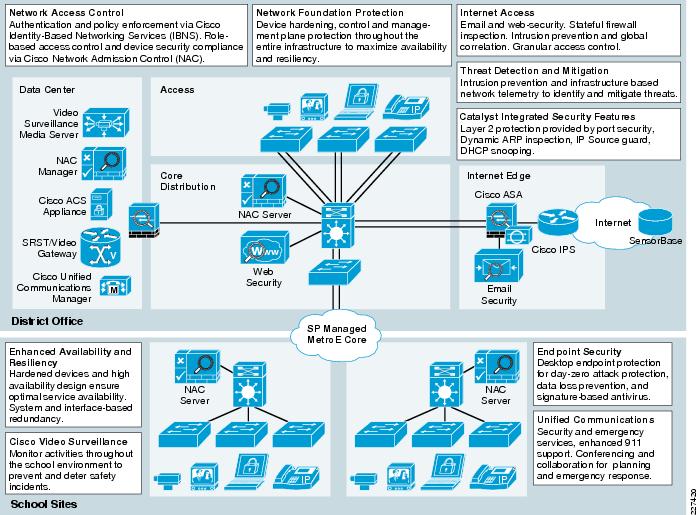
PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part II: Implementation and Evaluation

Vulnerabilities in Cisco Small Business routers could allow unauthenticated attackers persistent access to internal networks | The Daily Swig


![Security Best Practice to secure your Cisco Router and Switches | Learn [Solve IT] Security Best Practice to secure your Cisco Router and Switches | Learn [Solve IT]](https://i2.wp.com/techdirectarchive.com/wp-content/uploads/2020/05/980239e9-cisco-logo.jpg?fit=780%2C516&ssl=1)